Track all markets on TradingView
BREAKING NEWS
- ‘Happened very fast’: At least 10 killed, 11 injured in Brazil fire
- Israeli pressure delayed Freedom Flotilla’s departure for Gaza: Organisers
- UN warns of possible imminent attack on city in Sudan’s North Darfur
- Qatar pledges $3m to Ukrainian human rights body
- Arming genocide? New report documents use of US arms in Israeli war crimes
- Apple Could Reportedly Offer AI Features On-Device With iOS 18, But That Might Come at a Cost
- Apple Is Working on a New Feature for Apple Watch That Will Send Alerts if the User Is Drowning
- iPhone 16 Pro Cameras Tipped to Get New Anti-Reflective Technology to Help Reduce Lens Flare
- iOS 17.5 Beta 2 Brings Supports for Installing iPhone Apps via Websites: Report
- Microsoft OneNote App for Apple Vision Pro With Hands-Free Note Taking, Virtual Keyboard Support Launched
Latest Stories
Tech & Gadgets
How to turn your iPhone into instant foreign language translator
In today’s interconnected world, the ability to communicate across language barriers is more important than ever. Apple has recognized this…
Read More...
Read More...
How to remove Facebook access to your photos
Raise your hand if you’ve ever skimmed through the user agreements and legal jargon that appear when signing up for new software or…
Read More...
Read More...
Get a handle on your time: Google Calendar tips and tricks
Before we get into it, I’ll acknowledge what you may be thinking: Using Calendar means handing over even more info to Google.Win an iPhone…
Read More...
Read More...
New stealthy submarine glider set for autonomous undersea missions
The ocean depths are a new frontier explored by humans and autonomous vehicles.Leading the charge is Northrop Grumman's innovative Manta Ray…
Read More...
Read More...
AI-powered home security system strikes back with paintballs and tear gas
A company from Slovenia, called PaintCam, is shaking things up in the security world. It has come up with this wild new gadget, the…
Read More...
Read More...
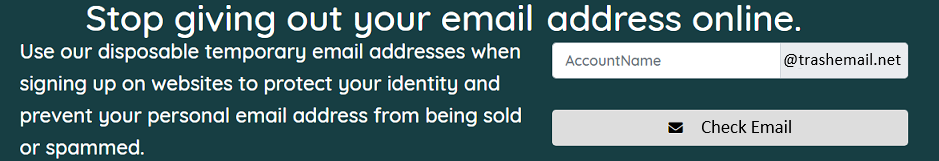
Tired of getting those mysterious password reset emails? Here’s what to do about it
Passwords can definitely be a frustrating part of our lives. Remembering which passwords you used for your dozens of different accounts is…
Read More...
Read More...
Fox News AI Newsletter: AI predicts your politics with single photo
The study used AI to predict people's political orientation based on images of expressionless faces. (American Psychologist)Welcome…
Read More...
Read More...
- Advertisement -